Home » Investors » Corporate Governance » Corporate Governance Practices » Information Security Organization Management
Corporate Governance Practices
Information Security Organization Management
In order to effectively implement the Company’s information security management, the Company has set up an information security team, with the CRO acting as the convener, and under which there are the information security response center and the information security implementation team, responsible for the information security management, planning, supervision, and execution facilitation to reduce the Company’s operation and information security risks. In order to implement the information security maintenance plan, the Company has added an information security audit team in 2023.
The Information Security Committee shall meet regularly each year to review and examine the implementation of the Company’s information security management policies and report its findings to the Board of Directors. The last report was made on November 2, 2023.
Information security audit team:
It shall be assigned by the Information Security Committee or assisted by a third party to evaluate the implementation of the information security management system.
Information Security Organizational Structure and Job Responsibilities:
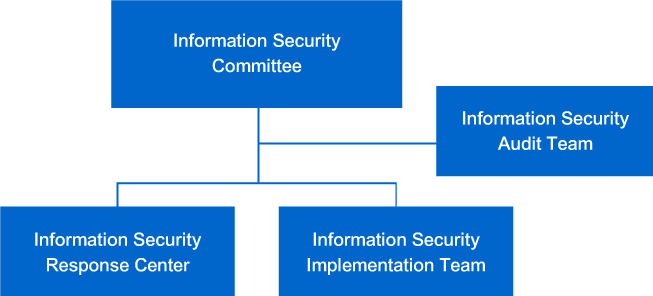
(1) Information Security Committee:
The CRO shall act as the convener of the committee, and the Information Security Response Center and the Information Security Implementation Team set under the committee are responsible for the implementation of resolutions related to the information security management system.
(2) Information Security Implementation Team:
The team is composed of the personnel assigned by the convener of the Information Security Committee that is responsible for planning and implementing various information security works.
(3) Information Security Response Center:
The Center is responsible for responding to unexpected information security events with corresponding solutions, as well as tracking collection and event identification. The “Risk Improvement Plan” shall be prepared, controlled, and tracked continuously until the improvement.
(4) Information security audit team:
It shall be assigned by the Information Security Committee or assisted by a third party to evaluate the implementation of the information security management system.
Information Security Policies and Specific Management
For the purposes of improving the security and stability of the Company’s information and communication, providing reliable information services, including the security precautions that must be controlled when using the network and information systems, preventing operational risks and hazards such as improper use, disclosure, tampering, and destruction of the Company’s information and data; and raising the awareness of information security on the clients, and the specific management measures are as follows:
| MANAGEMENT ITEM | MEASURE |
|---|---|
| Information Security Policy and Education Training | ● Formulate information security policy and raise information security awareness among employees through information security promotion |
| Network security management | ● Effectively manage the network environment according to operational requirements and security levels, and separate access control between internal and external network environments |
| System access control | ● Formulate system access control policy according to colleagues' business needs, specify the access authorization of users and personnel, and properly document the change process and preserve the records ● Separate the R&D from the general office environment to prevent unauthorized personnel from directly accessing confidential and sensitive data, and keep critical data from being disclosed |
| Terminal equipment management | ● Information security control for servers, PCs, and other devices, including software and hardware asset inventory, anti-virus, system patch update, and sensitive data access control |
| Data protection | ● Regularly schedule data preservation backups, including electronic files, documents, mail, server operating environment, personal computers, and network devices |
| Information Security Incident Management | ● Scan outsourced information system vulnerability and remedy vulnerability ● Provide solutions for unanticipated information security incidents, collect trace, and trace events to reduce the likelihood of occurrence and minimize operational impact |
Resources of Invested Information Security Management
The Information Security Committee meets regularly every year to examine and review the implementation status. The last time it was reported to the Board of Directors was on October 31, 2024. The information security incident in 2024 did not affect operations or goodwill. In addition, the ISO 27001 International Information Security Management Certification was obtained in 2024. The current certificate is valid from January 11,2024 to January 10, 2027.
Resources of Invested Information Security Management in 2024:
- Carry out information & communication security education and training, and through information security publicity and social engineering drills, enhance the information security awareness of colleagues.
- The access to the network environment is effectively partitioned and controlled based on operational requirements and security levels.
- Terminal device information security control, including software and hardware asset inventory, endpoint protection software (anti-virus), and data leakage protection.
- Outsource information system vulnerability scanning and fix bugs for vulnerabilities.
- Regularly schedule data preservation backup, including electronic files, documents, mails, server operating environment, personal computers, and network equipment.
- The manpower investment of information security includes one information security supervisor and several information security personnel, responsible for information and communication security management, planning, supervision, and promotion of execution, as well as information and communication security incident response and investigation.
- The Information Security Committee holds regular meetings annually to review matters related to the information & communication security management of the Company and the implementation of the information & communication security policies. The findings are then reported to the Board of Directors.
